An Update from Microsoft? No, a sneaky hunter for your money
Imagine an email dropped into your inbox. The email makes you a tempting offer: Updating your version of Microsoft Word to add new features. Do you think installing new features is a good idea? Of course, you do. Because you are curious about the new features. And more of that, they can even make your work more convenient and fun. So, you eagerly click on the Word file attached to the email and… you are trapped. You’ve just given away your computer at the mercy of the infamous trojan named Emotet.
This banking Trojan has become a pain in the neck for business companies and state institutions for years. Coming in different disguises, it invariably remains devastating by the attack consequences. The U.S. National Cybersecurity and Communications Integration Center called Emotet “one of the most costly and destructive malware affecting state, local, tribal, and territorial governments, and the private and public sectors”.
And now a new wave of Emotet attacks hit the computers around the world, this time disguised as a Microsoft Word update.
But why is Emotet considered so dangerous? Let’s see.
How Emotet can harm your computer
Emotet is a banking trojan, and, as it’s clear from this definition, is aimed at stealing financial-related information from the infected computers. Covertly running in the background, it steals banking credentials and other logins and passwords. Unfortunately, it does not stop there.
Emotet is also used to download other types of malware on the infected machine. Thus, an endpoint compromised by Emotet becomes open to never-ending infection. It totally goes under the attackers’ control, so they can use the infected machine as they want. They can steal, add or destroy data, turn the victim’s computer into a zombie as a part of a bot to attack other entities… actually, they can do anything, depending on their desire and imagination.
How Emotet spreads
The trojan is usually propagated via phishing email campaigns as an email attachment. It consists of two elements: Social engineering and implanting malware.
The first element is the content of the phishing emails specially crafted to lure users into running the malicious file. It changes with every wave of the Emotet attacks. In the past campaigns, it came in form of an “invoice’, a “letter from DHL”, “information about COVID-19”, etc. The freshest instances are disguised as Windows or Microsoft Word updates.
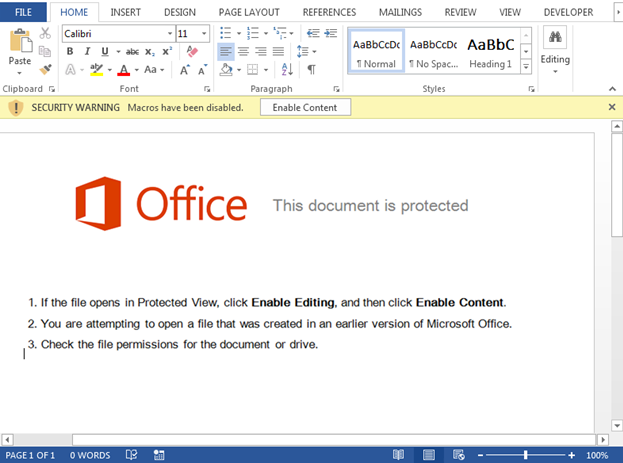
The second element is the attached Word document containing malicious Macros. Running this document starts the process of uploading Emotet on a victim’s computer.
How Emotet works
The malware needs user participation to infect a computer. Running the infected file is enough if macros in your Word are set to “allow”. If you are rather smart to not allow them by default, the malware will ask you to turn on this option to enable the file’s content.
If you buy this trick, the coast for Emotet is clear. The infecting processes will continue covertly without you even noticing it.
The malicious macro script rebuilds an obfuscated shellcode. Then PowerShell runs to download Emotet executable file from the attackers’ servers. After installing, it creates a service to provide its running with every system startup. Then Emotet sends a message about infecting a new victim to the attackers and remains to wait for their following commands. As we mentioned before, the range of commands is almost unlimited: From stealing banking credentials to turning the machine into a zombie on service of the cybercriminals.
There are two factors that make Emotet extremely dangerous and widespread.
Firstly, the way of spreading. People and companies can’t prevent changing Word files by email – otherwise, they just would not be able to work. And as cunning Social Engineering tricks are hard to resist for untrained people, many fall preys to the poisonous documents.
Secondly, Emotet has a special feature to hide from antimalware. Being polymorphic, it can easily bypass signature-based antivirus detection.
Thirdly, it does not stop after infecting a computer but tries to spread itself on all endpoints in the network.
How to protect from Emotet
In this case, the usual rules of cybersecurity hygiene are not enough. You can download files only from reliable sources, avoid visiting suspicious websites and have updated antivirus but it does not guarantee 100% protection from Emotet.
So, what can you do? Strike the weakest point, of course.
The weakest point of Emotet is the necessity of running macros. If they are not allowed, the infecting process won’t start and, consistently, Emotet won’t be able to do you any harm. Thus, check the macros are turned off in your Word by default and never turn them on in a Word document if you are not 100% sure of its reliability.
Live informed and secure with DIESEC!
